SecPoint
SecPoint Penetrator S9 - Vulnerability Scanning Pen Test Appliance
SecPoint Penetrator S9 - Vulnerability Scanning Pen Test Appliance
Regular price
$2,029.00 USD
Regular price
$1,420.30 USD
Sale price
$2,029.00 USD
Unit price
per
Shipping calculated at checkout.
Couldn't load pickup availability
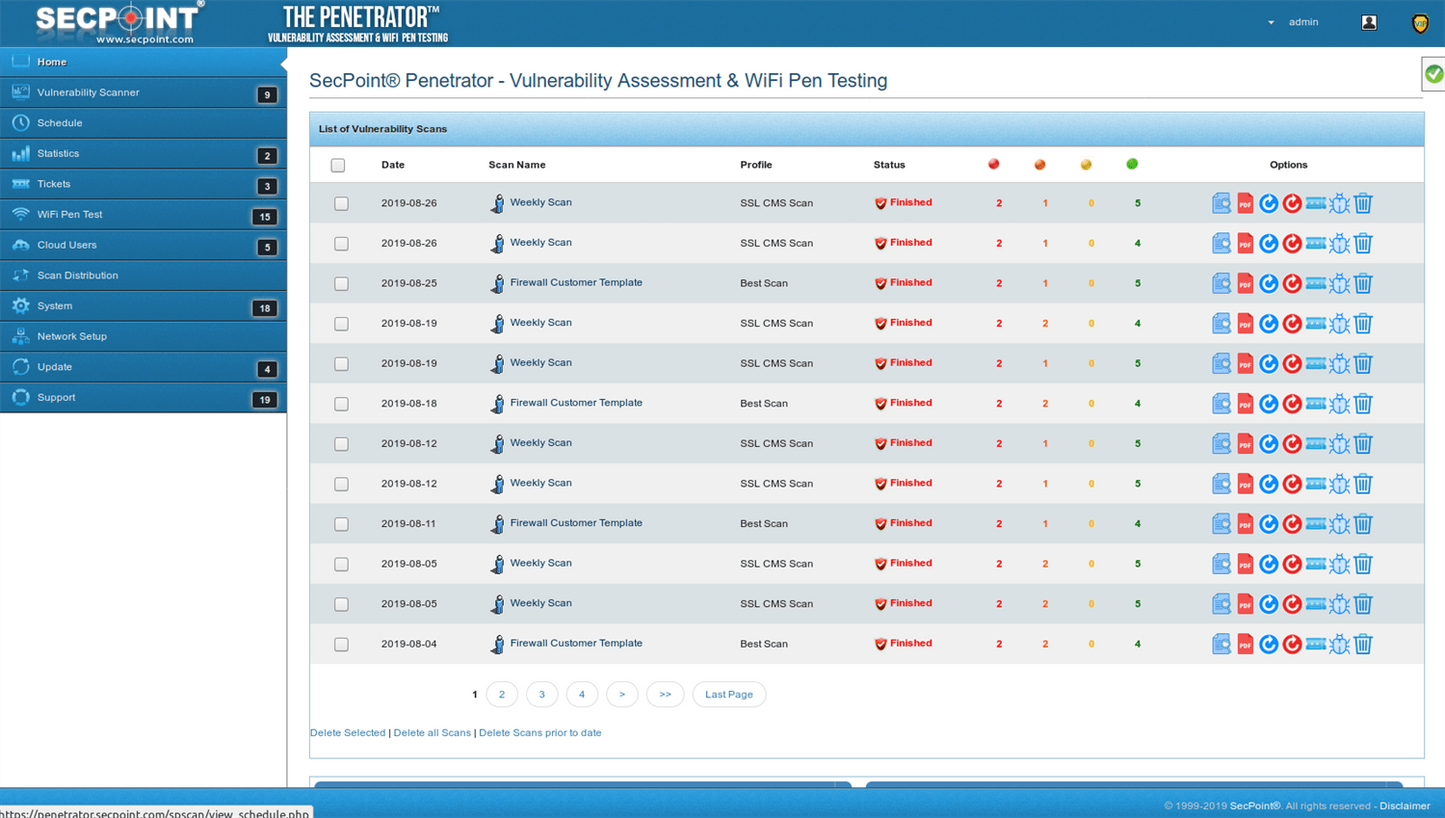
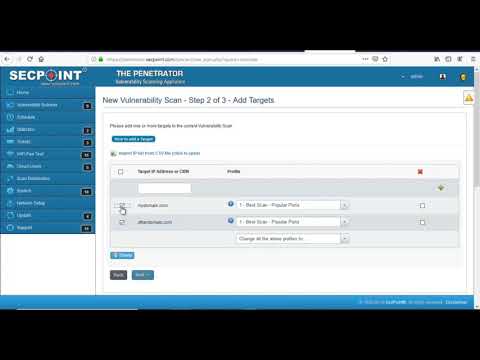
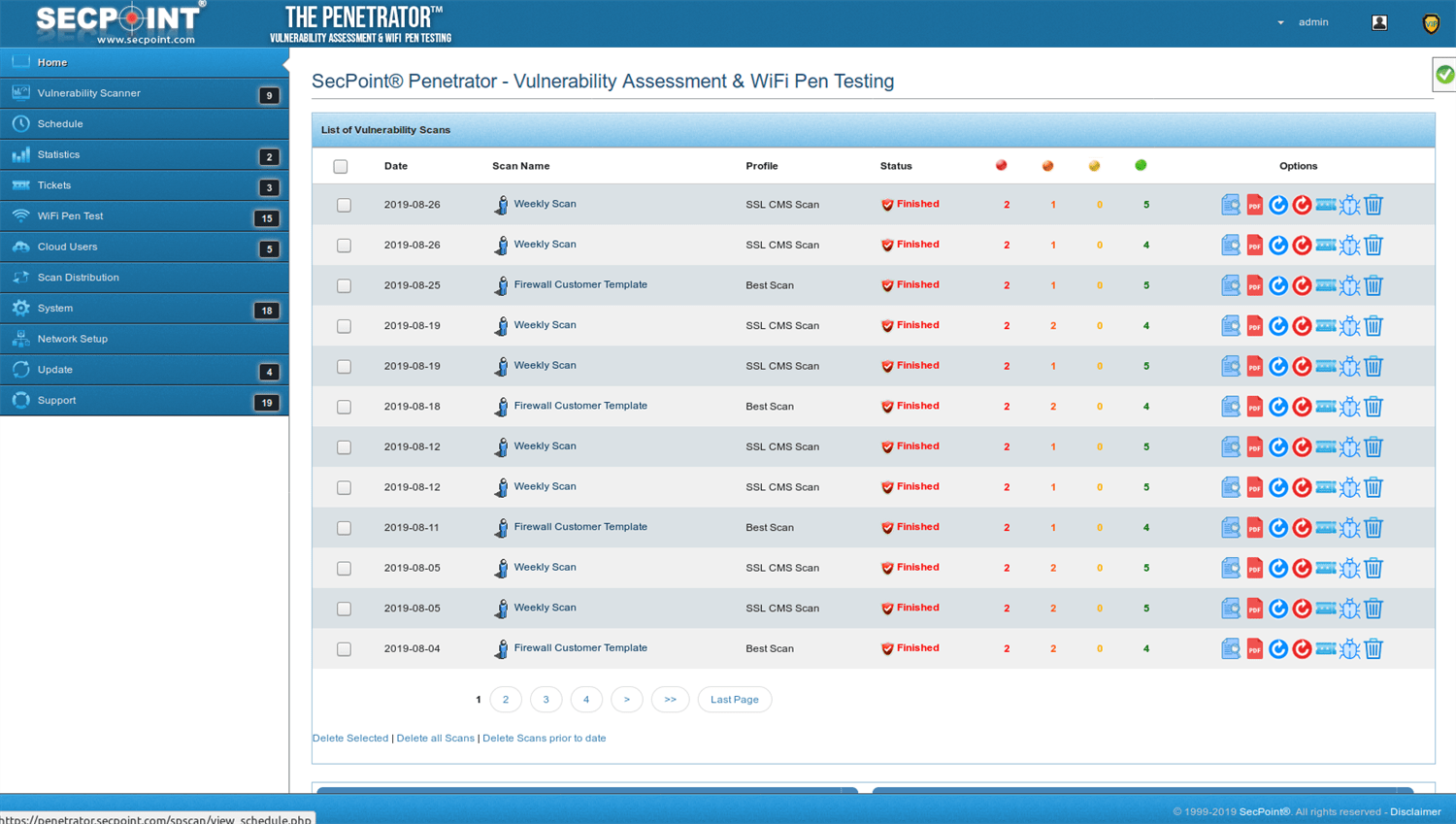
SecPoint Penetrator™ - Vulnerability Scanning - Cross Site Scripting, XSS, SQL Injection, Vulnerability assessment - with 1 Year Subscription and Support Bundle Scan your servers for vulnerabilities. Identify Vulnerabilities. An option to fix the found vulnerabilities. Automated Vulnerability Browsing and Auditing.
SecPoint® Penetrator™ key features:
- 143,000+ Vulnerability Checks
- 1,400+ Web Shells Detection
- Data Leak Detection
- Lethal Attack Technology
- Daily updated database
- 25 Report Languages
- 33 Vulnerability Scan Profiles
- Dark Web Search 4.0
- Easy to use GUI interface
- Advanced AI High Accuracy
- Easy scheduling of vulnerability scans
- Managed Service Provider (MSP)
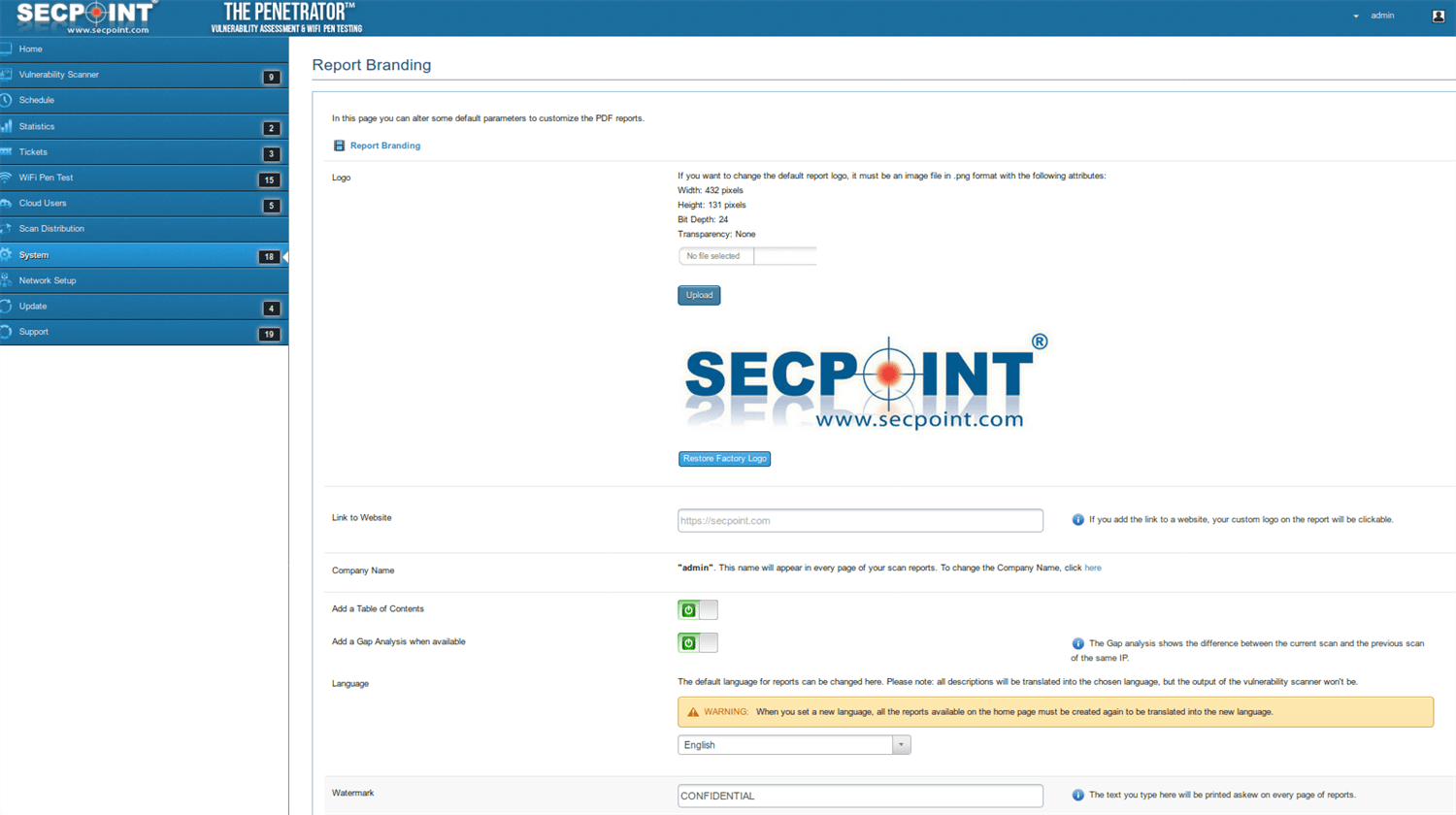
- Whitelabeling
- Notification on email about scan status
- Vulnerability Scanning & Assessment
- High Speed SSD Solid State Drive included.
- Scan local & public IPs
- SQL Injection, Blind SQL Injection
- Command Execution, Information Disclosure
- Cross Site Scripting (XSS)
- Reflected Cross Site Scripting
- Customize reporting with logo,name,watermark
- Notification by email when new vulnerabilities are discovered
- SecPoint® RBL List
- Block 640+ Million Toxic IPs
- SCADA & IoT Reveal vulnerabilities across your network. No experience necessary. Easy to Setup. Scans both public and local IP addresses. Discover vulnerabilities in Firewalls, Routers, Windows, Linux, MAC, Mobile devices, Printers and any device with an IP address. Custom PDF reporting that allows logo and name integration. Cloud support allows for individual user management. WiFi Adapter not included. Must be purchased separately for WiFi Pen testing functionality. Full Scanning of vulnerabilities in: Wordpress, Drupal, Joomla, Magento, Shopify, Umbraco. Do you know if your installation is wrongly configured or have applied the latest patches? Full scanning included in SecPoint Penetrator™. The only restriction is that you can optimum scan 32 IP addresses at the exact same time. You can easily transform them as a lot as you desire. - Individual friendly data system that will certainly reveal you scans compared by month so you could see in for example May compared to April how the quantity of vulnerabilities are expanding or coming to be less. - User pleasant open PDF files with advised answers for all located vulnerabilities. You can easily modify the PDF as you desire. - Multi user login support - Circulated bookkeeping. With Multiple home appliances you could link them with each other and browse different locations by remote. You can easily do daily, month-to-month or once a week safety scans of your IP addresses. The Scanning Engine has been established on for greater than THIRTEEN years. It consist of more than. The system produces complete PDF reports with solutions how to resolve the vulnerabilities. Secure your systems with: wpa2 crack - Vulnerability scan - wepcrack - Crack wifi - Wpa2 cracking - wifi crack SecPoint® Penetrator™ Brochure
SecPoint® Penetrator™ Datasheet SecPoint® Penetrator™ Output Example Report SecPoint® Penetrator™ Executive Report